Absolute for Cybersecurity and Compliance
Mitigate risk and strengthen your compliance posture with Absolute
Establish cyber resilience amid increasing threats
Modern enterprise infrastructures are made up of large and complex entities. They will always have flaws and weaknesses that adversaries will be able to exploit. In turn, cyber resilience is now top of mind when it comes to ensuring the entire workforce is using endpoints and network access in secure ways. In addition, ever-changing regulatory mandates make it difficult to get and stay compliant.
Focused on what matters to you
We are committed to providing solutions that meet the unique and evolving needs to enable your business
Add title here

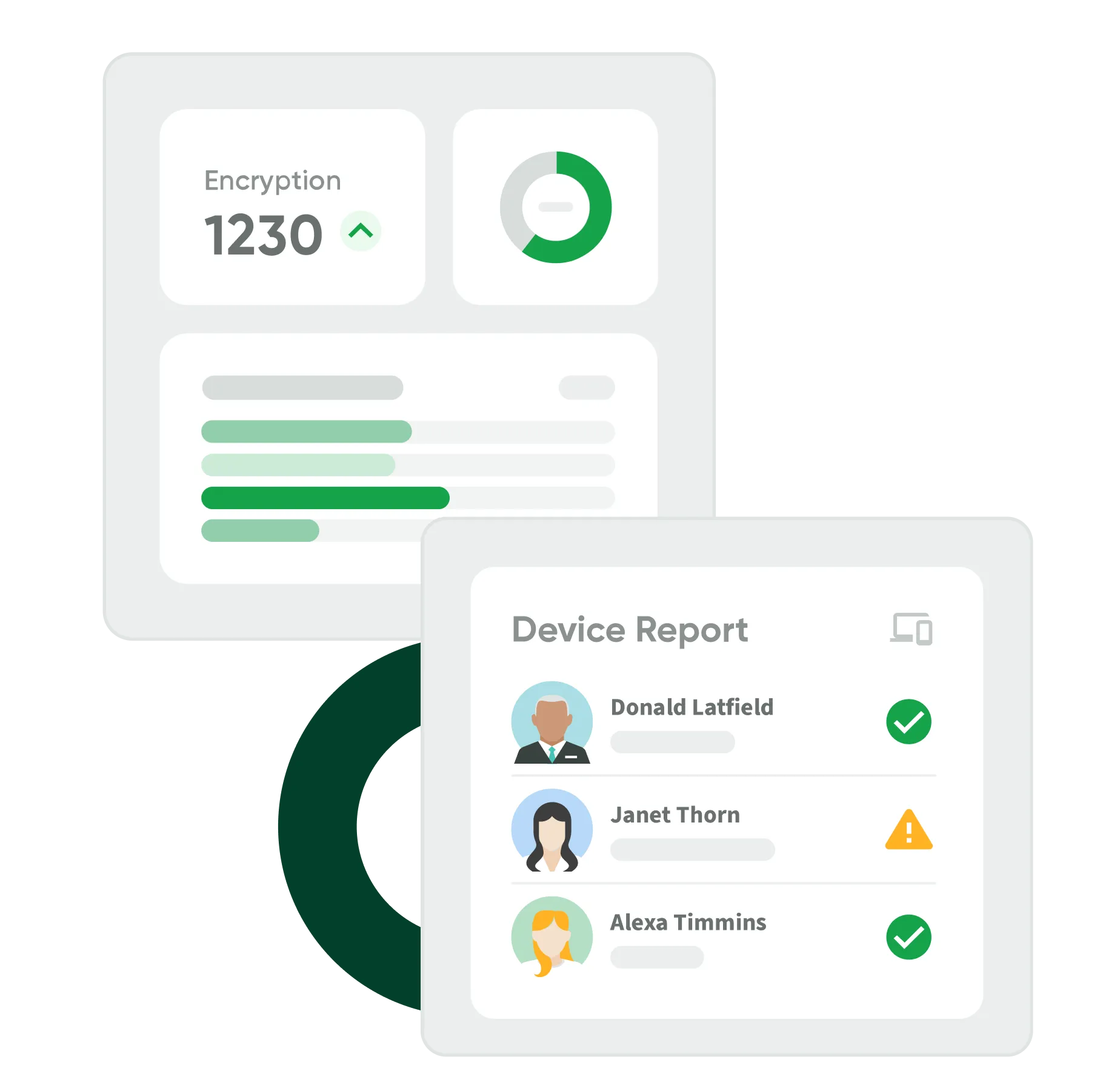
Assure security efficacy via self-healing
Add title here

Streamlined collection of compliance evidence
Add title here

Critical application availability and uptime for incident response
Add title here

Reduced mean time to response after vulnerability detection
Add title here

Easy enforcement of security configurations at scale
Add title here

Improved risk score
Absolute + CrowdStrike: Enterprise cyber resilience, better together
See how Absolute and CrowdStrike reduce downtime with unified protection, response, and rapid endpoint recovery at scale.

Learn how to solve your most challenging Cybersecurity and Compliance issues with Absolute
Secure Endpoint
Assess security posture
- Detect failing security applications
- Detect configuration deviations
- Detect vulnerable OS or applications
- Report on compliance with regulations and industry standards
Secure Endpoint
Enforce security standards
- Make security applications self-healing
- Enforce standard configurations
- Remediate vulnerable OS or applications
- Provide visibility for streamlined patch management workflow
Secure Endpoint
Identify security incidents
- Spot suspicious device use or movement
- Identify missing devices
- Sense device tampering
- Identify sensitive data at risk
Secure Endpoint
Respond to endpoint risks
- Remotely protect sensitive data files
- Investigate stolen or suspicious devices
- Remediate compromised devices
- Communicate effectively with end users to minimize exposure
Secure Endpoint
Successfully recover from incidents
- Avoid breach notifications after incidents
- Find root cause to prevent future similar events
- Aid recovery efforts (e.g., ransomware recovery)
- Check strategic ransomware preparedness
Secure Endpoint
Protect resources
- Shield SaaS, on-premises, or private cloud resources from intruders and attacks
- Treat resources equally, regardless of where they are hosted
- Block lateral movement between applications
- Conduct continuous real-time risk assessment
Secure Endpoint
Protect users
- Limit user exposure to online threats and inappropriate content
- Allow for complete control, inside and outside the firewall
- Block automatically phishing and smishing attacks
- Provide frictionless security via granular policy enforcement at the endpoint