Automate the remediation of security exposures
Security vulnerabilities and misconfigurations can crop up from a variety of sources such as the operating system, deployed software, network or firewall settings and weak passwords. Leverage automation to seamlessly identify and respond to exposures to ensure your attack surface is minimized.
Highlights
Absolute Resilience for Automation™, the highest edition of the Secure Endpoint product, offers automated remediation of operating system, software and security vulnerabilities to eliminate risk and reduce an organization’s attack surface. It combines all the capabilities of Absolute Visibility™, Absolute Control™, Absolute Resilience™ and Absolute Resilience for Security™ with two additional critical features, Remediate and Automate.

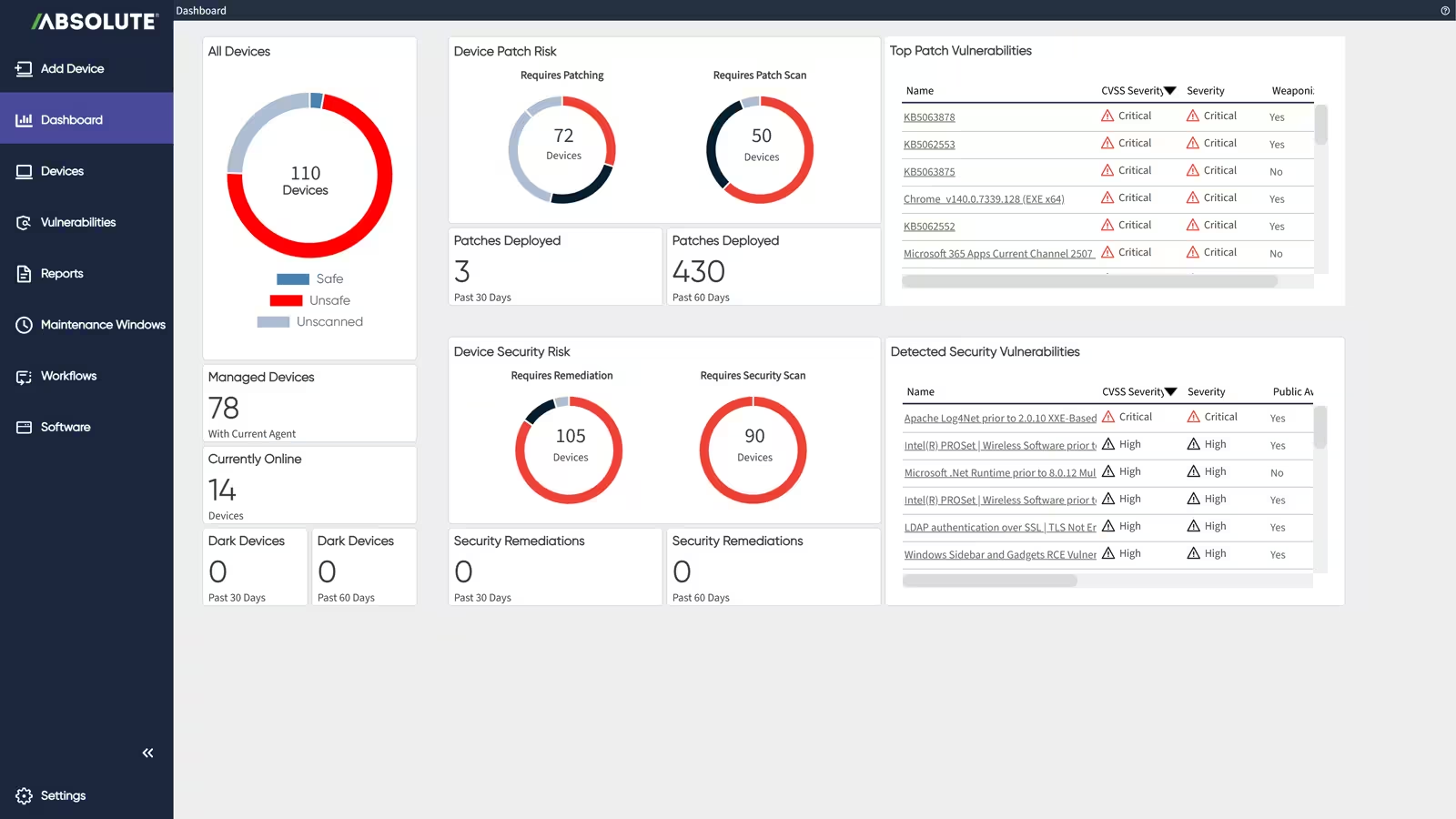
Scan for operating system, software and security vulnerabilities, misconfigurations, and blind spots to detect a potential breach before it occurs.

Access an extensive library of prebuilt remediation workflows for thousands of existing vulnerabilities to secure devices at the push of a button.

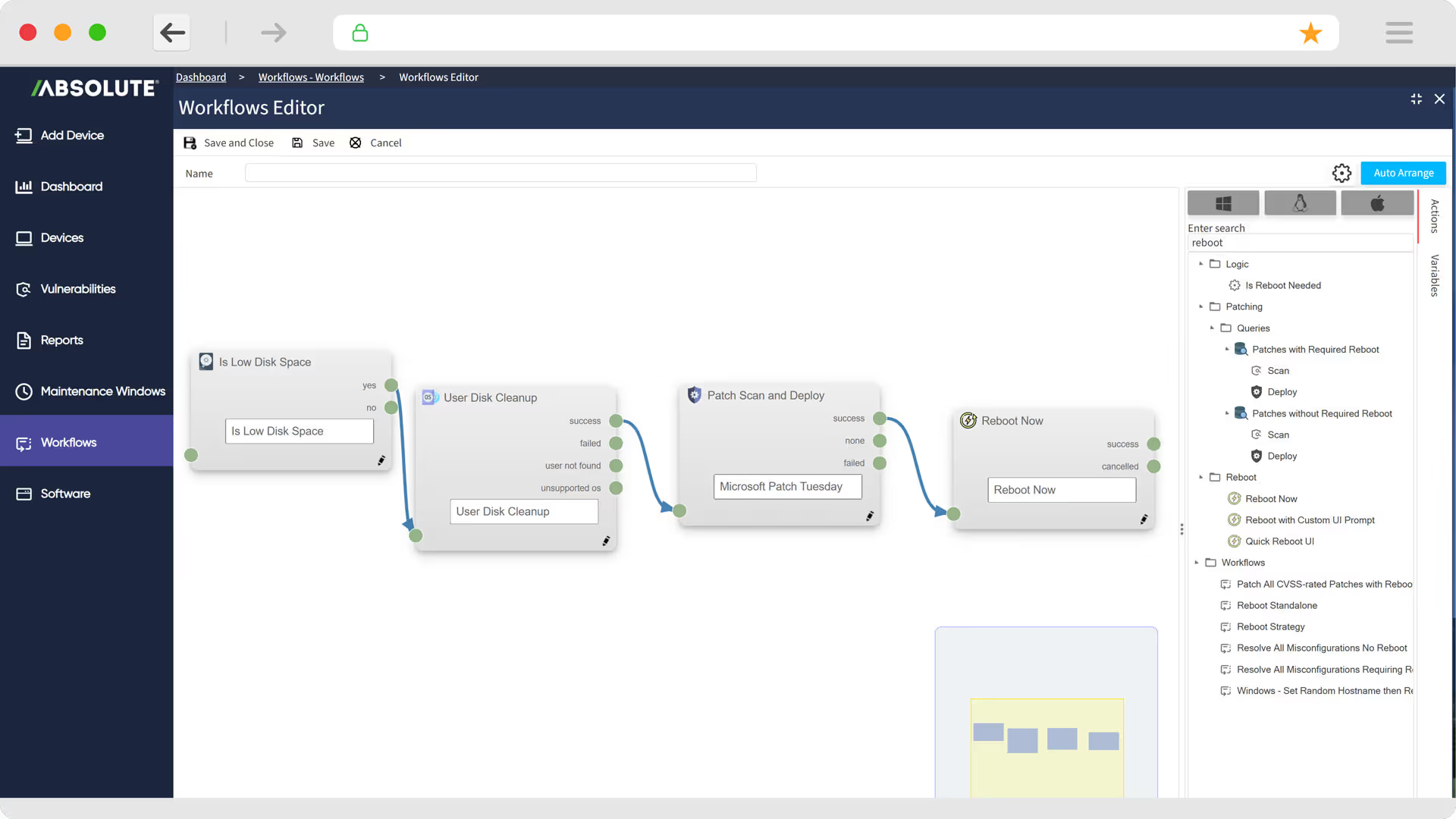
Visually define custom remediation workflows with multi-step actions using the intuitive automation workflow builder.

Swiftly react to disclosed vulnerabilities once patches are available to limit exposure.

Detect behavioral and state changes on endpoints in real-time and execute self-healing workflows to harden endpoints and improve compliance.

Support your business priorities with a risk-based patching and remediation approach.

Diagnose and fix device issues remotely, reducing downtime and improving mean time to resolution.

Remotely recover devices back to a fully trusted and compliant state to get your business back up and running faster and prevent lateral attack movement.

Obtain tailored endpoint, security and compliance information across your environment by asking questions to the Absolute AI Assistant.
Transform your CISO role from protection to resilience
Evolve your security strategy to deliver value in a new era of cyber risk with Gartner® Maverick research.
Identify and respond to security vulnerabilities
Minimize your attack surface that can be exploited
- Combine patch and vulnerability management using live, real-time data to eliminate both operating system vulnerabilities and security weaknesses.
- Access thousands of workflows for existing vulnerabilities directly through the Absolute Console as well as updated content as new vulnerabilities are discovered.
- Respond to a variety of other security weaknesses like user account misconfigurations, insecure passwords, out of date anti-virus or definitions, disabled firewalls and open ports.
- Discover devices over the network for enhanced attack surface monitoring.
- Customize risk scoring to support your business priorities with a risk-based approach.

Build automated remediation workflows
Leverage the intuitive workflow builder
- Visually define custom workflows using the automated workflow builder without requiring any coding. Deploy complex remediations that would otherwise require advanced scripting.
- Build multi-step actions using the builder to reestablish control and eliminate risk at the endpoint.
- Leverage the unique Persistence technology embedded in the firmware of PCs as well as a unique endpoint management architecture providing real time visibility to reliably scan for and respond to threats.
- Remotely access and control devices without being physically present to resolve user issues more efficiently.
- Utilize supplementary tools to troubleshoot and fix device issues.

Recover endpoints quickly
Accelerate endpoint recovery after an IT issue or cyberattack to a fully trusted and compliant state
- Firmware-based endpoint recovery playbooks bypass the operating system if tampered with, including options like rehydrating from a trusted OS image, modifying files/registry keys, and executing scripts.
- Passcode-protected “break-glass” mechanism runs at boot up to download and execute recovery playbooks, ensuring secure recovery.
- Management and status tracking of recovery playbooks through the Absolute Console, with role-based access controls for certified users.

What our customers love about Absolute Resilience

Our endpoint management systems have an important job to do, but they don’t provide us with the single source of truth that Absolute Secure Endpoint does. The fact that Absolute Secure Endpoint is integrated within the BIOS is a big advantage. We use Absolute Persistence® technology and Absolute Application Resilience™ for these deployments to ensure that mission-critical applications remain healthy and function as intended.
Simple and flexible packages
Discover how Absolute keeps your devices secure, resilient, and always connected.
Explore Secure Endpoint products

Serves as your source of truth for device and application health.

Provides you a lifeline to protect at-risk devices and data.

Delivers application self-healing and confident risk response.

Provides seamless and proactive patch management.

Offers remediation of security vulnerabilities through automated workflows.

Boosts ransomware preparedness and time-to-recovery.
Explore our products

Built from ground up for mobility and the modern edge.

Delivers the best user experience for the software-defined perimeter.

Comprehensive SSE provides security controls and threat protection across web, cloud, and private apps.

Boosts diagnostics and remediation for digital experience monitoring.

Web security that protects data, prevents threats, and secures access to cloud apps.
Related product packages
Specifically tailored capabilities for Chromebook users.
Specifically tailored capabilities for Windows student devices.
Specifically tailored capabilities for Education customers.
Featured resources
Secure Endpoint FAQ
Absolute Secure Endpoint is one of our company’s core product lines, which leverages the unbreakable connection provided by Absolute Persistence® to enable IT and security personnel to monitor and address computers' problems and enables the computers and their mission-critical applications to self-heal. This helps with IT management, strengthening a company’s security posture, and maintaining compliance.
The Absolute Secure Endpoint product portfolio contains a variety of product packages:
- Absolute Visibility
- Absolute Control
- Absolute Resilience
- Absolute Resilience for Security
- Absolute Resilience for Automation
- Absolute Ransomware Response
Other variants, such as Absolute Resilience for Student Devices, may be offered to meet particular use cases or geographic market needs.
Absolute Resilience is the third product edition in the Absolute Secure Endpoint product portfolio. Compared to Absolute Control, it adds further capabilities to secure endpoints from IT or security risks, respond to unexpected downtime due to security breaches and incidents, and enable Application Resilience to automatically monitor and detect unhealthy applications and automatically heal them.
Absolute Resilience for Security is the fourth product edition in the Absolute Secure Endpoint product portfolio. It combines all the capabilities of Absolute Visibility™, Absolute Control™ and Absolute Resilience™ with the Patch module, enabling IT and security teams to scan their endpoint population to assess patch health in relation to known operating system and software vulnerabilities.
Absolute Resilience for Automation is the highest product edition in the Absolute Secure Endpoint product portfolio, offering automated remediation of operating system, software and security vulnerabilities to eliminate risk and reduce an organization’s attack surface. It combines all the capabilities of Absolute Visibility™, Absolute Control™, Absolute Resilience™ and Absolute Resilience for Security™ with two critical features, Remediate and Automate.
Absolute Ransomware Response is a stand-alone offering, which provides capabilities and services to assess an organization's ransomware preparedness and cyber hygiene across endpoints; ensures mission-critical security applications such as anti-malware and device management tools remain healthy and capable of self-healing; and expedites the quarantine and recovery of endpoints if a ransomware attack occurs.
Customers can easily upgrade/downgrade their product subscriptions between Absolute Visibility, Control, Resilience, Resilience for Security and Resilience for Automation. Capabilities are additive and enabled via a software license key.
Absolute Ransomware Response is offered as a stand-alone solution primarily for security-conscious customers. Add-on options are offered for Absolute Control, Resilience, Resilience for Security and Resilience for Automation customers.
Absolute can be purchased through leading device manufacturers, resellers, and distributors. Contact us and we would be happy to help you with this process.